The request looked routine at first. The kind that usually comes and goes without leaving a mark.
But this one lingered.
Legal started pulling threads. And the deeper they dug, the worse it got. Emails missing. Documents gone cold. Files vanished without a trace, and no one who could say when, why, or who pulled the trigger.
What should have been routine turned into something else entirely: a credibility problem with teeth.
Defensible Disposition Key Takeaways:
- Defensibility is proven through consistent execution and documentation, not just a written policy.
- Addressing redundant, obsolete, and trivial (ROT) data is critical to reducing discovery costs and legal risk.
- Effective retention schedules require specific, trackable trigger events to ensure records aren’t kept indefinitely.
- Regular internal audits and documented destruction certificates are the primary evidence used to defend disposition actions.
Most organizations have a retention policy. On paper, at least. But when you look closer, the story changes. Fewer have developed a comprehensive defensible disposition framework, and that gap is where the trouble starts. Deleting records without a consistent process, proper authorization, and clear documentation might feel like routine cleanup, but it can look very different under the harsh light of legal scrutiny. Defensible disposition is the framework that ensures your organization lawfully and consistently destroys eligible records and non-records with a paper trail that holds up when the questions come.
What is Defensible Disposition?
Defensible disposition isn’t a single event. It’s a framework. One that either holds together under pressure… or doesn’t. It is the output of interlocking processes that must work together including a legally sound retention schedule, policies that cover everything you create (not just official records), consistent implementation across your systems and paper, regular auditing to catch drift, a solid litigation hold process, and a plan for when something goes wrong.
6 Step Defensible Disposition Framework
Step 1: Build a Retention Schedule You Can Actually Implement
Every disposition decision traces back to your retention schedule. If it’s incomplete, outdated, or impractical to apply, everything built on top of it becomes shaky.
First, it needs to reflect your organization, not a one-size-fits-all approach. Templates won’t capture the specifics of how you operate. If you manufacture regulated products, manage assets, or operate in a specialized or licensed environment, your schedule should reflect that. Just as important, it has to be written in a way your employees can navigate quickly. If people can’t find what they’re looking for, they won’t use it, and unclassified records quickly become unmanaged ones.
Second, it must account for the jurisdictions you operate in. Retention requirements vary widely, and organizations often underestimate how those differences stack up. In many cases, you’ll need to apply the most stringent requirement across jurisdictions or explicitly define exceptions. And this isn’t a “set it and forget it” exercise, laws and guidance change. A schedule that was accurate a year ago may already be outdated. Build regular review into your governance process and rely on current legal research, not static references.
Finally, every retention rule needs to be workable. That means clearly defining both the retention period and the trigger event that starts the clock. “Seven years for contracts” isn’t enough. Seven years from when? Execution? Expiration? Last activity? If the trigger isn’t clear, people fill in the gaps. And they don’t all fill them in the same way. And if the trigger can’t be tracked reliably, records tend to be kept indefinitely. A good test is simple: can your systems consistently identify the trigger date without requiring judgment calls?
Step 2: Beyond Records: Controlling ROT and Non-Record Content
Not everything your organization creates qualifies as a record. But that doesn’t mean it’s harmless. Left unmanaged, non-record content becomes its own kind of risk. Your Records and Information Management policy or your Retention Schedule needs to address this explicitly.
A major category here is ROT: redundant, obsolete, and trivial content. Think of duplicate files, outdated drafts, and low-value communications. Left unchecked, ROT increases discovery costs, slows systems, and makes it harder to find what matters. For many organizations, the biggest contributor is everyday communication. Emails, chats, and messages that serve a short-term purpose and then linger indefinitely. Your policy should define transitory, redundant, obsolete, and trivial content, explain when it is not treated as a record, and specify how routine deletion is authorized and carried out.
Not all information exists as documents, either. Data in systems like CRMs, ERPs, and databases don’t fit neatly into traditional retention categories. This is where process-driven retention comes into play. Instead of focusing on document types, you look at the business process behind the data and determine retention based on that. Your policy should map key systems to the processes they support, assign ownership, and define how disposition decisions are made and documented. If you don’t address this, large portions of your data environment remain effectively unmanaged.
Step 3: From Policy to Practice: Driving Adoption
A policy doesn’t matter if no one follows it. Defensibility isn’t about what’s written down. It’s about what actually happens day to day. That means embedding it in the systems where records live and supporting it with a repeatable process.
Start with individual-access systems like email, OneDrive, and local machines. These are often the least controlled environments, and they’re where both over-retention and accidental loss happen most frequently. You need clarity. What’s automated. What’s the user’s responsibility. And how you verify both. Because telling people what to do isn’t the same as making sure they do it.
Structured environments like SharePoint, document management systems, shared drives should be easier to control. In theory. In practice, they often aren’t. Sites multiply, structures drift, and retention controls aren’t applied consistently. Effective implementation means applying classification and retention rules at the point of creation or ingestion, not trying to clean things up later at scale. Periodic reviews help confirm that content is landing where it should and that outdated material is being removed as expected. And don’t forget paper records.
Paper records shouldn’t be overlooked. They carry the same legal weight as digital records, and they need to be included in your processes for storage, retrieval, and destruction. Otherwise, you’ve got a blind spot.
When records reach the end of the line, disposition follows a process. No guesswork. No shortcuts.
- Identify what’s eligible.
- Confirm the details.
- Get the right approval.
- Carry out destruction.
- Document everything.
That documentation, often in the form of a destruction certificate, is critical evidence that the process was followed properly.
Effective records management isn’t just about compliance, it directly benefits users when they understand its value. With strong training and ongoing communication, organizations can move beyond “check-the-box” habits and show how good practices save time, reduce risk, and make information easier to find. When users see how records management supports their daily work, they’re more likely to adopt it. The goal is to make it not just a requirement, but a clear advantage.
Step 4: Audit Before Someone Else Starts Asking Questions
A program that looks good on paper isn’t enough. You need to know it’s actually working. Regular audits are what turn policy into something defensible.
Formal audits should review how the retention schedule is being applied, whether records are stored appropriately, whether disposition workflows are followed, and whether documentation is consistently maintained. Findings should be tracked and resolved, and the audit trail itself becomes part of your compliance record.
Between formal audits, targeted spot checks can be just as valuable. Instead of trying to review everything, focus on specific systems, teams, or record types. For example, you might verify that retention labels in Microsoft 365 haven’t been altered, or that a newly onboarded group is correctly classifying records. These smaller checks help catch issues early, often before they become larger problems.
It also makes sense to trigger reviews based on events, not just schedules. System migrations, acquisitions, or major staffing changes are all points where governance can slip.
Step 5: Don’t Forget Litigation Holds
When litigation is reasonably anticipated, the clock starts ticking, whether anything’s been filed or not. At that point, routine deletion isn’t routine anymore. It stops. Routine disposition must be suspended for information within the hold’s scope until the hold is released.
Hold notices need to:
- Go out quickly;
- Be clear enough to act on;
- Be tracked so you know they were received and understood.
For ongoing matters, periodic reminders are standard.
Scope is a common weakness. A proper hold covers not just official records, but drafts, communications, and anything else that could be relevant. It also needs to be implemented at the system level. Automated deletions and lifecycle policies won’t stop on their own. They have to be explicitly suspended.
When the matter ends, the hold should be formally lifted and normal processes restored, with that transition documented just as carefully as the hold itself.
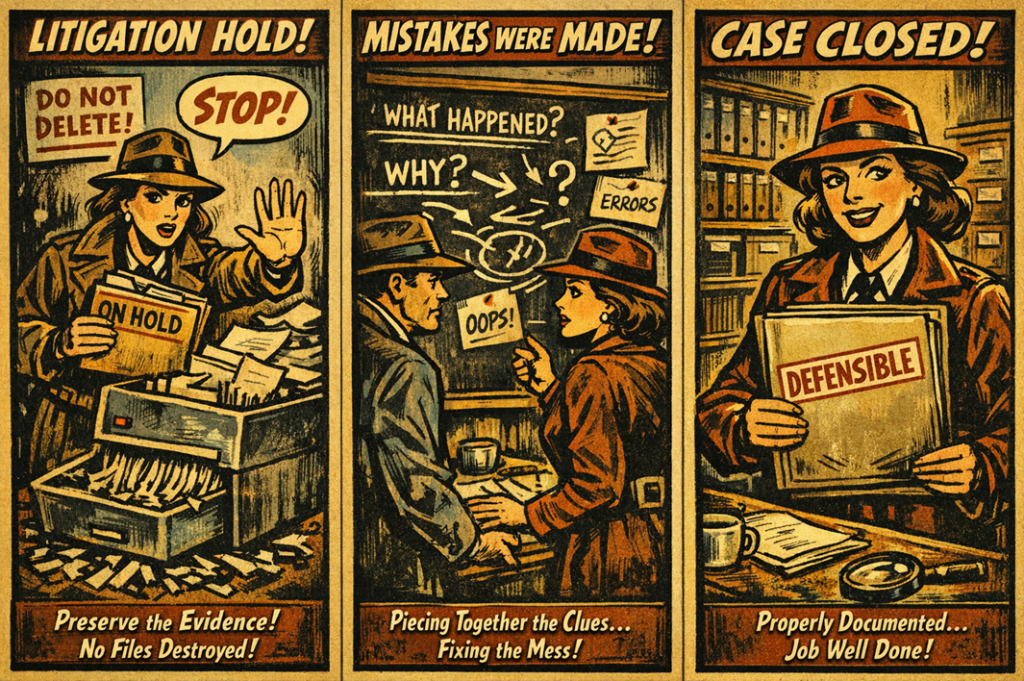
Step 6: When Things Go Wrong (Because Sometimes They Do)
Even well-designed programs run into issues. Missed holds, premature deletions, or system errors. What matters is how those situations are handled.
- The first step is to stop any related destruction and secure what remains.
- Then bring in the right stakeholders, often including legal, before taking action. Trying to fix things too quickly without proper guidance can make the situation worse.
- From there, conduct a documented investigation to understand what happened, when, and why.
- Determining whether the issue was inadvertent or intentional is critical, as that distinction carries different consequences. In some cases, the question of whether to self-report will arise. That decision typically sits with legal counsel, but in general, organizations that identify and address issues proactively tend to be viewed more favorably than those where problems emerge later through external discovery.
- Once resolved, address the root cause and document the fix.
That record becomes part of your overall compliance story.
Defensible Disposition Framework: Bringing It All Together
At its core, defensible disposition is about accountability. Knowing what you kept. What you destroyed. When it happened. And why. Because sooner or later, someone’s going to ask. And when they do, it won’t be about policy. It’ll be about proof. Being able to explain what you kept, what you destroyed, when it happened, and why. That doesn’t come from a single policy or tool, it comes from consistent execution over time.
The challenge isn’t just building the defensible disposition framework. It’s maintaining it through system changes, staff turnover, and competing priorities. And that’s exactly the point. You’re both building this for routine operations and for the moment when someone comes knocking, asking you to explain a record that no longer exists. When that happens, your documentation, your processes, and your consistency are what determine whether it’s a routine matter or something much more serious.
Disclaimer: The purpose of this post is to provide general education on information governance topics. The statements are informational only and do not constitute legal advice. If you have specific questions regarding the application of the law to your business activities, you should seek the advice of your legal counsel.